What’s in your jQuery app? Not the fishy ‘jquery-lh’ we hope!
The popular jQuery project has a mysterious sidekick that has popped – ‘jquery-lh’. While the npm package does install real jQuery code, behind the scenes it does something fishy and unexpected.
jQuery is ubiquitous when it comes to websites and web apps. On npm, the real jQuery project attracts over 4,000,000 weekly downloads.
What better project to capitalize on for a threat actor than jQuery? And that brings us to ‘jquery-lh,’ an attempt at brandjacking a famous open source project.
jquery-lh: not a jQuery module
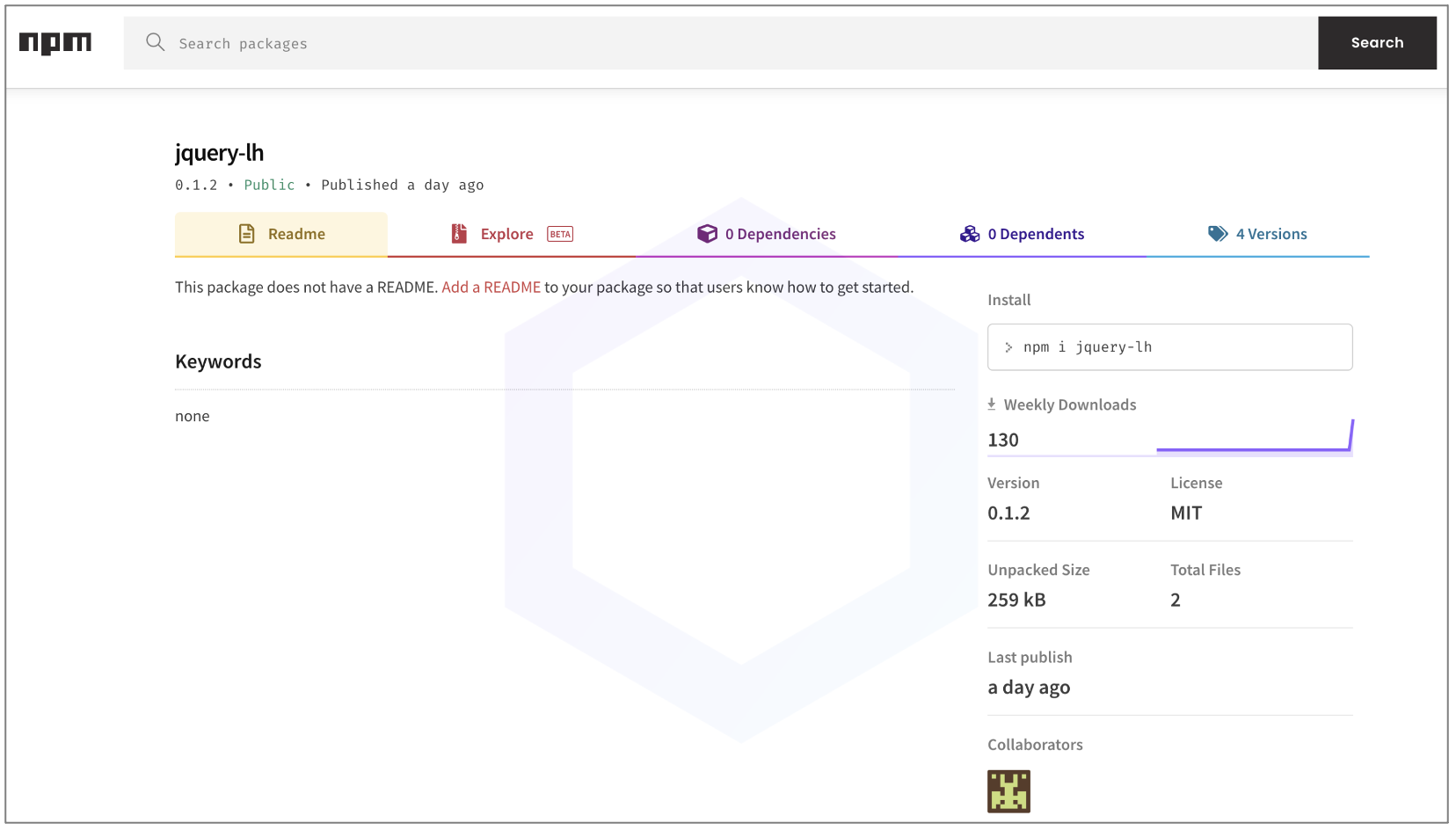
This morning, Sonatype’s malware detection bots caught ‘jquery-lh,’ an npm package that has managed to score just a little over 100 downloads so far. The package is tracked under sonatype-2022-1005 in our security research data.
‘jquery-lh’ comes in just 4 versions: 0.1.2, 3.846.2, 2.545.2, and 1.544.2—all released yesterday that are identical in their structure and purpose.
The manifest file, package.json in these packages implies that “dist/jquery.js” is the main file that runs on launch. And, to an extent, that’s true. The JS file contains functional jQuery code and packed modules commonly seen in legitimate web applications.
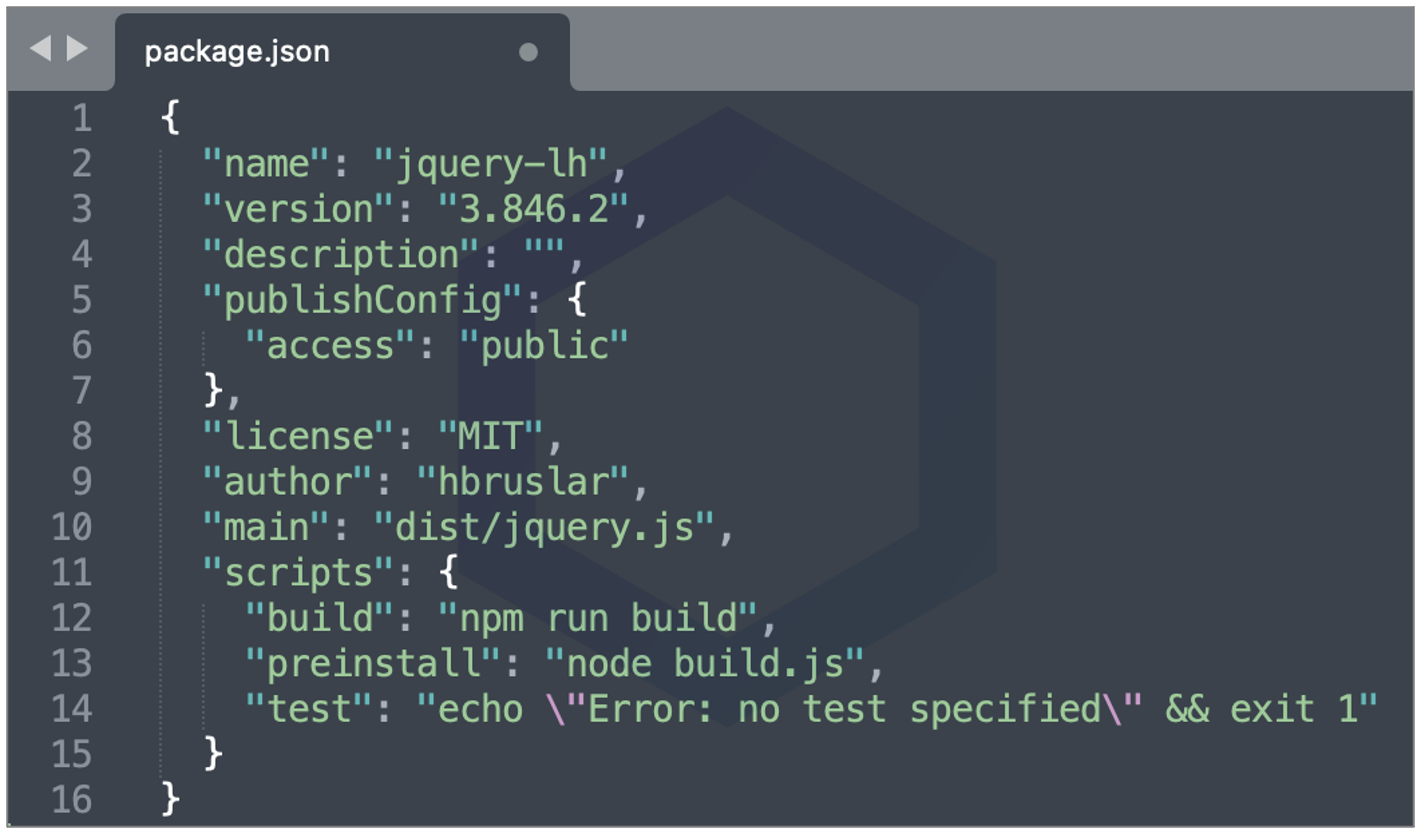
But, it’s the “preinstall” script build.js that’s the culprit running a suspicious piece of code behind the scenes, as soon as the npm package is pulled into your system.
While ‘lh’ may mean ‘line-height’ in the context of front-end development involving Bootstrap and jQuery, ‘jquery-lh’ has got nothing to do with line heights.
On line 17, the script peeks into your process.env, a known provisioning mechanism for accessing system variables, such as PATH.

But further, the package mysteriously checks (on lines 18-25) if any of your environment variables, such as PATH, contain one or more key-value pairs specified in the ‘filter’ object. And if that (Read more…)
Read more here: Source link






